Fashionable-day vulnerability administration tends to observe a simple process. From a excessive stage, this may be summed up within the following steps:
- Determine the vulnerabilities in your surroundings
- Prioritize which vulnerabilities to deal with
- Remediate the vulnerabilities
When high-profile vulnerabilities are disclosed, they are typically prioritized attributable to considerations that your group will likely be hammered with exploit makes an attempt. The overall impression is that this malicious exercise is highest shortly after disclosure, then decreases as workarounds and patches are utilized. The thought is that we ultimately attain a essential mass, the place sufficient methods are patched that the exploit is now not price making an attempt.
On this state of affairs, if we had been to graph malicious exercise and time, we find yourself with what’s sometimes called a long-tail distribution. A lot of the exercise happens early on, then drops off over time to type a protracted tail. This seems one thing like the next:
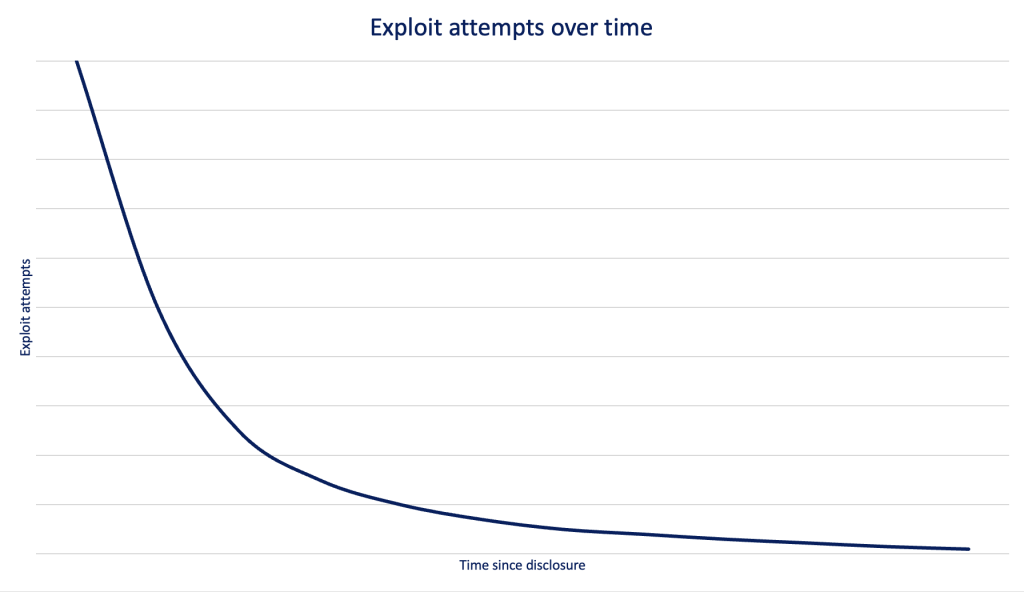
A protracted tail distribution of exploit makes an attempt sounds cheap in idea. The window of usefulness for an exploit is widest proper after disclosure, then closes over time till dangerous actors transfer on to different, newer vulnerabilities.
However is that this how exploitation makes an attempt actually play out? Do attackers abandon exploits after a sure stage, shifting on to newer and extra fruitful vulnerabilities? And if not, how do attackers strategy vulnerability exploitation?
Our strategy
To reply these questions, we’ll take a look at Snort knowledge from Cisco Safe Firewall. Many Snort guidelines defend in opposition to the exploitation of vulnerabilities, making this knowledge set to look at as we try and reply these questions.
We’ll group Snort guidelines by the CVEs talked about within the rule documentation, after which take a look at CVEs that see frequent exploit makes an attempt. Since CVEs are disclosed on totally different dates, and we’re alerts over time, the precise timeframe will fluctuate. In some instances, the disclosure date is sooner than the vary our knowledge set covers. Whereas we gained’t be capable of study the preliminary disclosure interval for these, we’ll take a look at a number of of those as effectively for indicators of a protracted tail.
Lastly, a rely of rule triggers will be deceptive—a number of organizations can see many alerts for one rule in a short while body, making the numbers look bigger than they’re throughout all orgs. As a substitute, we’ll take a look at the share of organizations that noticed an alert. We’ll then break this out on a month-to-month foundation.
Log4J: The 800-pound gorilla
The Log4J vulnerability has dominated our vulnerability metrics because it was disclosed in December 2021. Nonetheless, trying on the proportion of exploit makes an attempt every month since, there was neither a spike in use proper after disclosure, nor a protracted tail afterwards.

That first month, 27 p.c of organizations noticed alerts for Log4J. Since then, alerts have neither dropped off nor skyrocketed from one month to the subsequent. The p.c of organizations seeing alerts vary from 25-34 p.c by way of June 2023, averaging out at 28 p.c monthly.
Maybe Log4J is an exception to the rule. It’s a particularly frequent software program element and a extremely popular goal. A greater strategy is likely to be to take a look at a lesser-known vulnerability to see how the curve seems.
Spring4Shell: The Log4J that wasn’t
Spring4Shell was disclosed on the finish of March 2022. This was a vulnerability within the Spring Java framework that managed to resurrect an older vulnerability in JDK9, which had initially been found and patched in 2010. On the time of Spring4Shell’s disclosure there was hypothesis that this could possibly be the subsequent Log4J, therefore the similarity in naming. Such predictions did not materialize.

We did see a good quantity of Spring4Shell exercise instantly after the disclosure, the place 23 p.c of organizations noticed alerts. After this honeymoon interval, the share did decline. However as an alternative of exhibiting the curve of a protracted tail, the odds have remained between 14-19 p.c a month.
Eager readers will discover the exercise within the graph above that happens previous to disclosure. These alerts are for guidelines protecting the preliminary, more-than-a-decade-old Java vulnerability, CVE-2010-1622. That is attention-grabbing in two methods:
- The truth that these guidelines had been nonetheless triggering month-to-month on a 13-year-old vulnerability previous to Spring4Shell’s disclosure gives the primary indicators of a possible lengthy tail.
- It seems that Spring4Shell was so just like the earlier vulnerability that the older Snort guidelines alerted on it.
Sadly, the time-frame of our alert knowledge isn’t lengthy sufficient to say what the preliminary disclosure section for CVE-2010-1622 regarded like. So since we don’t have sufficient info right here to attract a conclusion, what about different older vulnerabilities that we all know had been in heavy rotation?
ShellShock: A basic
It’s onerous to consider, however the ShellShock vulnerability not too long ago turned 9. By software program improvement requirements this qualifies it for senior citizen standing, making it an ideal candidate to look at. Whereas we don’t have the preliminary disclosure section, exercise stays excessive to this present day.

Our knowledge set begins roughly seven years after disclosure, however the proportion of organizations seeing alerts ranges from 12-23 p.c. On common throughout this timeframe, about one in 5 organizations see ShellShock alerts in a month.
A sample emerges
Whereas we’ve showcased 3-4 examples right here, a sample does emerge when different vulnerabilities, each previous and new. For instance, right here is CVE-2022-26134, a vulnerability found in Atlassian Confluence in June 2022.

Right here is ProxyShell, which was initially found in August 2021, adopted by two extra associated vulnerabilities in September 2022.

And right here is one other older, generally focused vulnerability in PHPUnit, initially disclosed in June 2017.

Is the lengthy tail wagging the canine?
What emerges from vulnerability alerts over time is that, whereas there may be typically an preliminary spike in utilization, they don’t seem to say no to a negligible stage. As a substitute, vulnerabilities stick round for years after their preliminary disclosure.
So why do previous vulnerabilities stay in use? One motive is that many of those exploitation makes an attempt are automated assaults. Dangerous actors routinely leverage scripts and purposes that enable them to rapidly run exploit code in opposition to a big swaths of IP addresses within the hopes of discovering susceptible machines.
That is additional evidenced by trying on the focus of alerts by group. In lots of instances we see sudden spikes within the complete variety of alerts seen every month. If we break these months down by group, we frequently see that alerts at one or two organizations are chargeable for the spikes.
For instance, check out the full variety of Snort alerts for an arbitrary vulnerability. On this instance, December was in step with the months that preceded it. Then in January, the full variety of alerts started to develop, peaking in February, earlier than declining again to common ranges.

The reason for the sudden spike, highlighted in gentle blue, is one group that was hammered by alerts for this vulnerability. The group noticed little-to-no alerts in December earlier than a wave hit that lasted from January by way of March. It then utterly disappeared by April.
It is a frequent phenomenon seen in total counts (and why we don’t draw traits from this knowledge alone). This could possibly be the results of automated scans by dangerous actors. These attackers might have discovered one such susceptible system at this group, then proceeded to hammer it with exploit makes an attempt within the months that adopted.
So is the lengthy tail a delusion in terms of vulnerabilities? It definitely seems so—at the least in terms of the forms of assaults that concentrate on the perimeter of a company. The general public going through purposes that reside right here current a big assault floor. Public proof-of-concept exploits are sometimes available and are comparatively simple to fold into attacker’s present automated exploitation frameworks. There’s little danger for an attacker concerned in automated exploit makes an attempt, leaving little incentive to take away exploits as soon as they’ve been added to an assault toolkit.
What’s left to discover is whether or not long-tail vulnerabilities exist in different assault surfaces. The very fact is that there are totally different lessons of vulnerabilities that may be leveraged in several methods. We’ll discover extra of those sides sooner or later.
It solely takes one
Discovering that one susceptible, public-facing system at a company is a needle-in-a-haystack operation for attackers, requiring common scanning to search out it. However all it takes is one new system with out the most recent patches utilized to provide the attackers a possibility to realize a foothold.
The silver lining right here is {that a} firewall with an intrusion prevention system, like Cisco Safe Firewall, is designed particularly to stop profitable assaults. Past IPS prevention of those assaults, the not too long ago launched Cisco Safe Firewall 4200 equipment and seven.4 OS carry enterprise-class efficiency and a number of latest options together with SD-WAN, ZTNA, and the power to detect apps and threats in encrypted site visitors with out decryption.
Additionally, if you happen to’re in search of an answer to help you with vulnerability administration, Cisco Vulnerability Administration has you lined. Cisco Vulnerability Administration equips you with the contextual perception and risk intelligence wanted to intercept the subsequent exploit and reply with precision.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safe Social Channels
Share: