After I take a look at the evolution of community safety and the way IT and safety practitioners have protected the community for the final 30 years, I can’t assist however discover how conventional community safety enforcement factors (insert your favourite firewall right here) are nonetheless used to safe networks and workloads. They’ve advanced to supply a various set of options (i.e., IPS, decryption, software detection) to deeply analyze visitors coming out and in of the community to guard workloads. Nevertheless, whereas firewalls are very succesful home equipment, it has been confirmed that they don’t seem to be sufficient to maintain malicious actors at bay, particularly if these actors handle to breach the firewall defenses and transfer laterally within the community. However why is that this?
We’re within the digital period, the place the idea of the perimeter is now not contained to a location or a community section. To offset this new actuality and supply a extra tailored-based coverage management for safeguarding workloads, distributors have moved safety nearer to the workload.
There are two approaches to do that -, utilizing agent or agentless strategies to construct a micro-perimeter across the workloads.
Which method is the proper one to take? Properly, this is determined by a number of elements, together with organizations, kind of software, or group construction. So, let’s begin untangling this.
The problem(s)
Probably the most direct method to guard purposes is to put in software program brokers on each workload and name it a day. Why? As a result of then each workload has its personal micro-perimeter, permitting entry to solely what is important.
Nevertheless, it isn’t at all times attainable to put in a software program agent. Maybe it’s a mainframe software or a legacy working system that requires fine-grained insurance policies attributable to a compliance mandate. Or software workloads which might be within the cloud and the agent set up is just not attainable attributable to organizational constraints.
And this isn’t the one problem or consideration for selecting your method. The groups or teams that comprise any firm usually have totally different safety necessities from one another, resulting in the triad problem: folks, processes, and expertise.
Let’s begin with folks (coverage proprietor) and course of (coverage execution). Often, every group has its personal set of distinctive necessities to guard its software workloads, and an outlined course of to implement these necessities within the coverage. To assist this, a device (expertise) is required, which should adapt to every group’s wants and ought to be able to defining a typical coverage throughout agent and agentless workloads.
To start out unwrapping this, it’s good to ask your self:
- What are we defending?
- Who’s the proprietor of the insurance policies?
- How is coverage execution achieved?
For example:
Say you need to defend a finance software (what) utilizing an agent-based method (how), and the proprietor of the insurance policies is the App Group/Workload Group (who). On this situation, so long as the applying doesn’t break and the group can proceed to deal with coding, that is usually an appropriate method. Nevertheless, when implementing the widespread coverage, the interpretation from human language to machine language tends to generate additional guidelines that aren’t essentially required. This can be a widespread byproduct of the interpretation course of.
Now, let’s assume that in your group the safety of a legacy software (what) is tasked to the Community/NetSec group (who) utilizing an agentless enforcement method with community firewalls (how) as a result of on this case, it isn’t attainable to put in software program brokers because of the unsupported legacy working system. As within the first instance, additional guidelines are generated. Nevertheless, on this case, these pointless additional guidelines create destructive penalties due to firewall guidelines auditing necessities for compliance mandates, although they’re a part of the widespread coverage.
Topology because the supply of fact – pushing solely what’s required
Cisco Safe Workload has been addressing the folks, course of, and expertise challenges since its inception. The answer embraces each approaches – putting in software program brokers on workloads no matter type issue (bare-metal, VM, or container) or by utilizing agentless enforcement factors comparable to firewalls. Safe Workload adapts to every group’s wants by defining the coverage, such a zero belief microsegmentation coverage, to successfully apply micro-perimeters to software workloads in assist of the zero belief method. All inside a single pane of glass.
Nevertheless, as defined within the instance above, we nonetheless wanted to align our coverage to the compliance wants of the Community/NetSec group, solely utilizing the coverage guidelines which might be required.
To deal with the extra guidelines problem, we requested ourselves, “What’s the best strategy to push insurance policies right into a community firewall utilizing Safe Workload?”
The reply boiled all the way down to a typical idea for Community/NetSec groups – the community topology.
So how does it work?
With Safe Workload, the time period topology is intrinsic to the answer. It leverages the topology idea utilizing a assemble named “Scopes”, that are completely infrastructure agnostic, as proven in Determine 1.
It means that you can create a topology tree in Safe Workload primarily based on context, the place you may group your purposes and outline your coverage by utilizing human intent. For instance, “Manufacturing can not speak to Non-Manufacturing” and apply the coverage following the topology hierarchy.
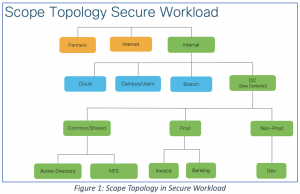
The Scope Tree is the topology of your software workloads inside the group, however the hot button is that it may be formed for various departments or organizational wants and tailored to every group’s safety necessities.
The idea of mapping a workload Scope to a community firewall is known as “Topology Consciousness.”
Topology Consciousness permits the Community/NetSec groups to map a selected Scope to a particular firewall within the community topology, so solely the related set of insurance policies for a given software is pushed to the firewall.
So, what does this execution appear like? With the Scope mapping achieved, Safe Workload pushes the related coverage to the Cisco Safe Firewall by the use of its administration platform, Safe Firewall Administration Middle (FMC). To take care of compliance, solely the required coverage guidelines are despatched to FMC, avoiding the additional pointless guidelines due to Topology Consciousness. An instance of that is proven in Determine 2:

Key takeaways
Operationalizing a zero belief microsegmentation technique will not be trivial, however Safe Workload has a confirmed observe file of creating this a sensible actuality by adapting to the wants of every persona comparable to Community/NetSec admins, Workload/Apps house owners, Cloud Architects, and Cloud-Native engineers – all from one resolution.
With topology consciousness, you may:
- Meet compliance and audit necessities for firewall guidelines
- Defend and leverage your present funding in community firewalls
- Operationalize your zero belief microsegmentation technique utilizing each agent and agentless approaches
For extra info on agentless enforcement please learn: Safe Workload and Safe Firewall Unified Segmentation Weblog
Wish to be taught extra? Discover out extra at by testing our Safe Workload assets.
We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Related with Cisco Safe on social!
Cisco Safe Social Channels
Share: